Foundations of information security
Pro vyhledávací frázi Foundations of information security jsme na našem vyhledávači našli 783 výsledků. Nenašli jste přesně to, co jste hledali? Zkuste frázi Foundations of information security trochu pozměnit a opět zadat do vyhledávacího pole. Pevně věříme, že produkt, který hledáte v naší nabídce na srovnávači CoChceš.cz naleznete!
Foundations Of Information Security
A comprehensive overview of the information security field.
Více informacíFoundations of Library and Information Science
In the fifth edition of this classic textbook, Richard E. Rubin and new co-author Rachel G. Rubin provide a foundational text for LIS students and pro
Více informacíNetwork Security and Cryptography
The definitive guide to the principles and techniques of cryptography and network security, and introduces basic concepts in computer networks such as
Více informacíInformation Security Management
Information security cannot be effectively managed unless secure methods and standards are integrated into all phases of the information security life
Více informacíInformation Security Governance
This book presents a framework to model the main activities of information security management and governance. The same model can be used for any secu
Více informacíCrafting an Information Security Playbook
Written by members of Cisco's Computer Security Incident Response Team, this book shows IT and information security professionals how to create an Inf
Více informacíInformation Security Risk Assessment Toolkit
Provides a defendable analysis of residual risk associated with your key assets so that risk treatment options can be explored. This title gives you t
Více informacíInformation Technology Security and Risk Management
Information Technology Security and Risk Management: Inductive Cases for Information Security is a compilation of cases that examine recent developmen
Více informacíFoundations of Manual Lymph Drainage
Covering the anatomy, physiology, and pathophysiology of the lymphatic system, this guide provides the information necessary for effective treatment.
Více informacíCloud Computing Basics
Highlights the recent developments in distributed computing and details the architecture, virtualization concepts, and security concerns of cloud comp
Více informacíCybersecurity for Information Professionals
The book is an introduction to essential concepts of cybersecurity and information security and the methods and techniques used to combat cybersecurit
Více informacíIntroduction to Machine Learning with Applications in Information Security
This class-tested textbook will provide in-depth coverage of the fundamentals of machine learning, with an exploration of applications in information
Více informacíInformation Security Education - Adapting to the Fourth Industrial Revolution
This book constitutes the refereed proceedings of the 15th IFIP WG 11.8 World Conference on Information Security Education, WISE 2022, held in Copenha
Více informacíSound Foundations Pack New Edition
Sound Foundations is an ideal introduction to the English phonological system and an invaluable resource both for teachers of full pronunciation courses and for those who sould ismply like to improve the quality of their work on pronunciation. It offers information on pronunciation systems as well as practical activities which can be used in pronunciation classes and in r...
Více informacíSafety and Security at Sea
Concerned with the safe operation of ships and preventing errors and oversights, this book provides information on safety where it is most effective -
Více informacíArt of Deception
Focusing on the human factors involved with information security, this book explains why all the firewalls and encryption protocols in the world will
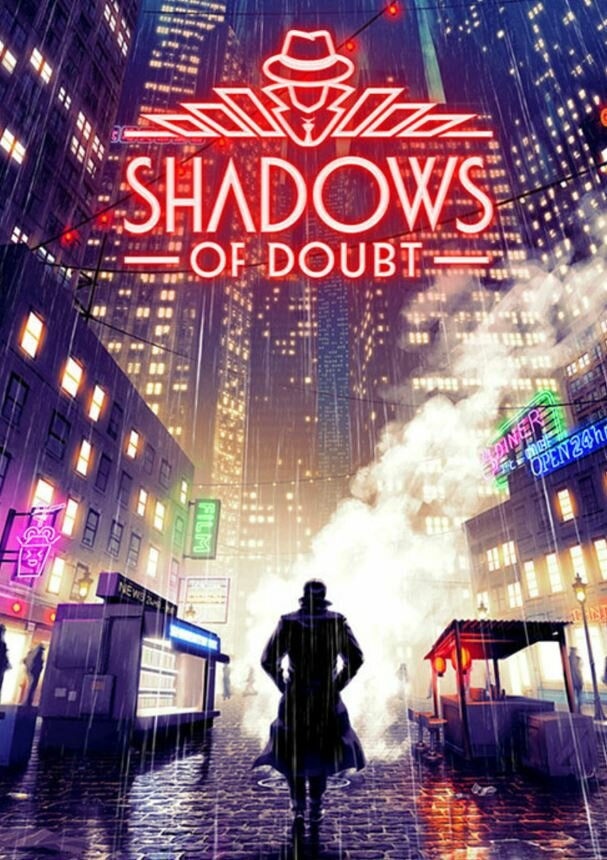
Více informacíShadows of Doubt (PC)
Early Access GameNote: This Early Access game is not complete and may or may not change further.A procedurally-generated sandbox stealth game with a whole city of secrets at your fingertips!Shadows of Doubt is set in an alternate reality in the hyper-industrialized 1980s. Think like a detective and use a variety of gadgets as a private intelligence investigator, ...
Více informacíShadows of Doubt
Early Access Game Note: This Early Access game is not complete and may or may not change further. A procedurally-generated sandbox stealth game with a whole city of secrets at your fingertips! Shadows of Doubt is set in an alternate reality in the hyper-industrialized 1980s. Think like a detective and use a variety of gadgets as a private intelligence investigator, g...
Více informacíEvolution of Business in the Cyber Age
The Evolution of Business in the Cyber Age: Digital Transformation, Threats, and Security provides a wealth of information for those involved in the d
Více informacíThe Inmate: From the Sunday Times Bestselling Author of The Housemaid - McFadden Freida
Anotace: A gripping, twisty thriller from Freida McFadden, the New York Times author of The Housemaid and The Coworker!The guiltiest people aren`t always the ones behind bars...As a new nurse practitioner at a maximum-security prison, Brooke Sullivan is taught three crucial rules: Treat all prisoners with respect.Never reveal any personal information. Never EVER become t...
Více informacíThe Inmate: From the Sunday Times Bestselling Author of The Housemaid - Freida McFadden
<p>A gripping, twisty thriller from Freida McFadden, the New York Times author of The Housemaid and The Coworker!The guiltiest people aren't always the ones behind bars...As a new nurse practitioner at a maximum-security prison, Brooke Sullivan is taught three crucial rules: Treat all prisoners with respect.Never reveal any personal information. Never EVER become to...
Více informacíBS ISO/IEC 27014:2013 31.5.2013
Platná norma BS ISO/IEC 27014:2013 Information technology. Security techniques. Governance of information security.
Více informacíBS 7799-1:1999 15.5.1999
Neplatná norma BS 7799-1:1999 Information security management. Code of practice for information security management.
Více informacíBS 7799UserDesktopVersion(A5PK5):1999 15.5.1999
Neplatná norma BS 7799UserDesktopVersion(A5PK5):1999 Information security management. Code of practice for information security management.
Více informacíLong-Term Psychodynamic Psychotherapy
This edition offers research on the foundations, techniques, and efficacy of psychodynamic psychotherapy, while still providing the information on ass
Více informacíGOST R ISO/IEC 27003-2012 1.12.2013
Platná norma GOST R ISO/IEC 27003-2012 Information technology. Security techniques. Information security management systems. Implementation guidance of information security management system
Více informacíISO/IEC 27002-ed.2.0 25.9.2013
Platná norma ISO/IEC 27002-ed.2.0 Information technology -- Security techniques -- Code of practice for information security controls
Více informacíISO/IEC 27014-ed.1.0 23.4.2013
Platná norma ISO/IEC 27014-ed.1.0 Information technology -- Security techniques -- Governance of information security
Více informacíBS ISO/IEC 17799GERMANTRANS. 1.1.1900
Platná norma BS ISO/IEC 17799GERMANTRANS. Information technology. Security techniques. Code of practice for information security management.
Více informacíBS 7799-1:1995 15.2.1995
Neplatná norma BS 7799-1:1995 Information security management. Code of practice for information security management systems.
Více informacíGOST R ISO/IEC 27002-2012 1.1.2014
Platná norma GOST R ISO/IEC 27002-2012 Information technology. Security techniques. Code of practice for information security management
Více informacíGOST 7.81-2001 1.7.2002
Platná norma GOST 7.81-2001 System of standards on information, librarianship and publishing. Statistical registration of non-periodical and periodical publications. Main foundations
Více informacíISO/IEC 27036-4-ed.1.0 28.9.2016
Platná norma ISO/IEC 27036-4-ed.1.0 Information technology - Security techniques - Information security for supplier relationships - Part 4: Guidelines for security of cloud services
Více informacíBS ISO/IEC 27036-4:2016 31.10.2016
Platná norma BS ISO/IEC 27036-4:2016 Information technology. Security techniques. Information security for supplier relationships. Guidelines for security of cloud services.
Více informacíGOST R 53109-2008 1.10.2009
Platná norma GOST R 53109-2008 Information security of the public communications network providing system. Passport of the organization communications of information security
Více informacíGOST R 56838-2015 1.11.2016
Platná norma GOST R 56838-2015 Health informatics. Information security management for remote maintenance of medical devices and systems. Part 2. Implementation of an information security management system
Více informacíETSI GS ISI 003-V1.1.1 13.5.2014
Platná norma ETSI GS ISI 003-V1.1.1 Information Security Indicators (ISI); Key Performance Security Indicators (KPSI) for the evaluation of maturity detection of security events
Více informacíISO/IEC/TR 19791-ed.2.0 22.3.2010
Platná norma ISO/IEC/TR 19791-ed.2.0 Information technology -- Security techniques -- Security assessment of operational systems
Více informacíISO/IEC 19792-ed.1.0 30.7.2009
Platná norma ISO/IEC 19792-ed.1.0 Information technology -- Security techniques -- Security evaluation of biometrics
Více informacíGOST R ISO/IEC TR 19791-2008 1.10.2009
Platná norma GOST R ISO/IEC TR 19791-2008 Information technology. Security techniques. Security assessment of operational systems
Více informacíUNE-ISO/IECTR 19791:2013IN 30.4.2013
Platná norma UNE-ISO/IECTR 19791:2013IN INFORMATION TECHNOLOGY. SECURITY TECHNIQUES. SECURITY ASSESSMENT OF OPERATIONAL SYSTEMS
Více informacíGOST R 57628-2017 1.1.2018
Platná norma GOST R 57628-2017 Information technology. Security techniques. Guide for the production of Protection Profiles and Security Targets
Více informacíGOST R ISO/IEC 17799-2005 1.1.2007
Neplatná norma GOST R ISO/IEC 17799-2005 Information technology. Code of practice for information security management
Více informacíR 50.1.111-2016 1.6.2017
Platná norma R 50.1.111-2016 Information technology. Cryptographic data security. Password-based protection of key information
Více informacíGOST R 53114-2008 1.10.2009
Platná norma GOST R 53114-2008 Protection of information. Information security provision in organizations. Basic terms and definitions
Více informacíBS ISO/IEC 13335-1:2004 13.12.2004
Neplatná norma BS ISO/IEC 13335-1:2004 Information technology. Security techniques. Management of information and communications technology security. Concepts and models for information and communications technology security management.
Více informacíDIN ISO/IEC 13335-1:2006-11 1.11.2006
Neplatná norma DIN ISO/IEC 13335-1:2006-11 Information technology - Security techniques - Management of information and communications technology security - Part 1: Concepts and models for information and communications technology security management.
Více informacíETSI GS ISI 008-V1.1.1 22.6.2018
Platná norma ETSI GS ISI 008-V1.1.1 Information Security Indicators (ISI); Description of an Overall Organization-wide Security Information and Event Management (SIEM) Approach
Více informacíISO/IEC 27002-ed.2.0/Cor.2 6.11.2015
Platná norma ISO/IEC 27002-ed.2.0/Cor.2 Corrigendum 2 - Information technology -- Security techniques -- Code of practice for information security controls
Více informacíISO/IEC 27006-ed.3.0 30.9.2015
Platná norma ISO/IEC 27006-ed.3.0 Information technology - Security techniques - Requirements for bodies providing audit and certification of information security management systems
Více informacíISO/IEC/TS 27008-ed.1.0 14.1.2019
Platná norma ISO/IEC/TS 27008-ed.1.0 Information technology - Security techniques - Guidelines for the assessment of information security controls
Více informacíISO/IEC 27035-1-ed.1.0 28.10.2016
Platná norma ISO/IEC 27035-1-ed.1.0 Information technology - Security techniques - Information security incident management - Part 1: Principles of incident management
Více informacíPodobné fráze: foundations of sports coaching | foundations of adult nursing | foundations of machine learning | acoustical foundations of music | foundations of art therapy | foundations of art and design | foundations of early childhood | new foundations of labour law | foundations of surface science | foundations of data science | foundations of nursing practice | foundations of scalable systems | foundations of modern slavery | foundations of marketing 7e | foundations of chinese medicine | legal foundations of capitalism | foundations of software testing | foundations of factor analysis | foundations of earth science | foundations of stage makeup | foundations of aviation law | foundations of safety science | foundations of computer science | foundations of financial risk | foundations of social research | technical foundations of iot | foundations of engineering ise | foundations of modern analysis | foundations of chemical biology | freedom of information officer s handbook | politics of freedom of information | fundamentals of information systems | the information sounds of the backwoods | trucking in the age of information | ethics law and the politics of information